A continuous list of Trojans being discovered worldwide in the last few years has left smartphone users feeling utterly helpless. The latest Trojan to join the list is a powerful one, going by the name of Dark Caracal or Dark Lynx. The shocking discovery of the malware has been made by Lookout, a mobile security company, and The Electronic Frontier Foundation (EFF).
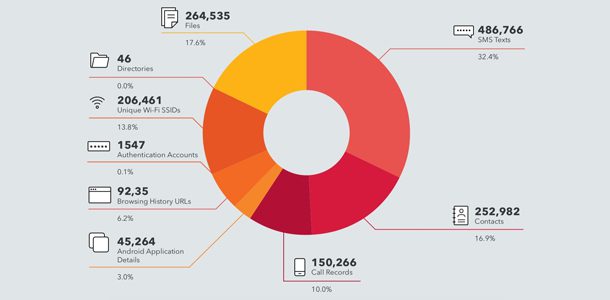
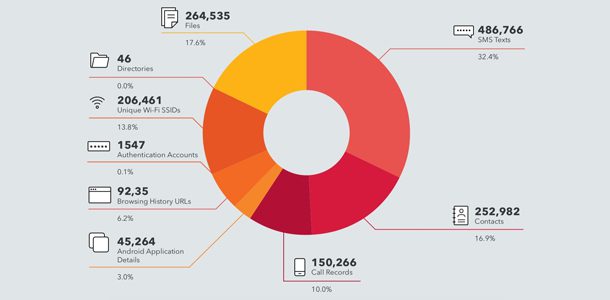
Dark Caracal has been in use since as late 2012, and over the last 5 years, it has been used to monitor the phones of journalists, lawyers, officials, military personnel, and activists, in over 20 countries worldwide. Messaging apps like WhatsApp, Orbot TOR Proxy, Signal, Primo, Threema, and Psiphon have been specifically targeted by the malware, which presents itself as clones of the aforementioned apps. When the user downloads these Trojanised apps, they can detect no difference since these apps perform like their normal versions. Simultaneously, however, these apps allow the attacker to receive information about texts exchanged, and allow them to gather photos, audio recordings, and location information.
One of the interesting things about this ongoing attack is that it doesn’t require a sophisticated or expensive exploit. Instead, all Dark Caracal needed was application permissions that users themselves granted when they downloaded the apps, not realizing that they contained malware. This research shows it’s not difficult to create a strategy allowing people and governments to spy on targets around the world. – Cooper Quentin, EFF’s Staff Technologist
Russia, Germany, USA, Great Britain, China, and India are some of the countries that have been targeted by the malware, and reports suggest that it is one among a large number of global attackers partaking in cyber espionage.




